Naming Convention
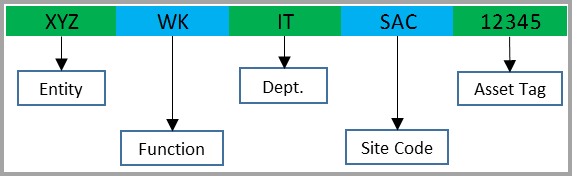
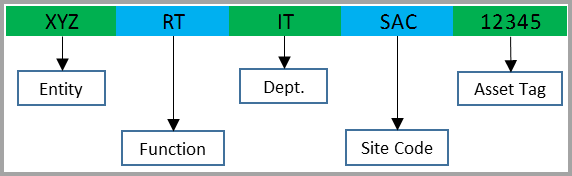
Naming Standards for Workstations and Laptops:¶
- Objects in this classification include: Workstations, Desktops, Laptops, Tablet PC’s, and windows mobile devices. Windows still has a 15 character limit for NetBIOS names, so this example is designed to maintain that limit.
- Objects in this classification will be named using the following breakdown.
| Position | Description |
|---|---|
| 1-3 | Entity. For objects under control of the |
| 4-5 | Functions Code. This code described the role of the device. The authorized options within this category are:MD - Mobile DeviceNB - Notebook / Laptop computerNX - Notebook / Laptop non-Domain Member (requires ISO Approval memo)TC - Thin Client Computing DeviceWK - Workstation / Desktop computerWX - Workstation non-Domain Member (requires ISO Approval memo) |
| 6-7 | Department. The 2 digit code that identifies the activity within the entity assigned the device for usage. If the device is a shared device, then the primary agency responsible for its proper usage will be identified. |
| 8-10 | Site Code. The 3 digit code identifies the city. Here is a good reference for CA city name codes Each state should have a state government website with similar codes. This site has some cities with 4 character abbreviations, but in order to maintain the overall consistency with other areas of this document, use only 3 characters. |
| 11-15 | Asset Tag. The 5 digit code that reflects the official |
Example Computer Name
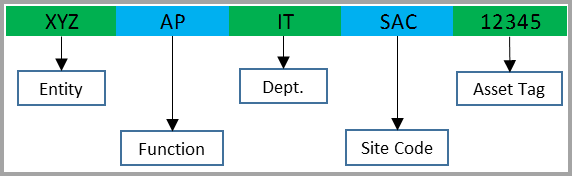
Naming Standards for Servers:¶
- Objects in this classification include server role names.
- Objects in this classification will be named using the following breakdown.
| Position | Description |
|---|---|
| 1-3 | Entity. For objects under control of the |
| 4-5 | Functions Code. The authorized options in this category are:AP - Application ServerAV - Anti-Virus ServerBE - Back End Mail ServerBG - Backup Gateway ServerBH - Bridgehead Mail ServerCA - Certificate Authority ServerDB - Database ServerDC - Domain ControllerDF - Distributed File System (DFS) ServerDH - Dynamic Host Configuration Protocol (DHCP)DN - Domain Name ServiceFE - Front End Mail ServerFS - File ServerFX - Fax ServerGA - Gateway / Bridge ServerGC - Global Catalog ServerLS - List ServerMD - Mobile DeviceML - Mail ServerMQ - Message Queue ServeGC - Global Catalog ServerML - Mail ServerMS - Media ServerNM - Network Management ServerPS - Print ServerPX - Proxy ServerRA - Remote Access ServerSM - System Management ServerSE - Security ServerWS - Web ServerVM - Voice MessagingVP - Voice Processor |
| 6-7 | Department – The 3 digit code that identifies the activity or agency assigned the device for usage. If the device is a shared device, then the primary agency responsible for its proper usage will be identified. |
| 8-10 | Site Code. The 3 digit code identifies the city. Here is a good reference for CA city name codes: http://www.dot.ca.gov/hq/structur/strmaint/brlog/table_c.htm This site has some cities with 4 character abbreviations, but in order to maintain the overall consistency with other areas of this document, use only 3 characters. |
| 11-15 | Asset Tag. The 5 digit code that reflects the official |
Example Server Name
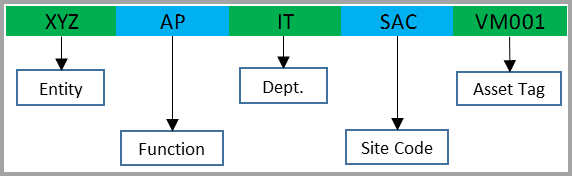
Naming Standards for Virtual Servers:¶
- Objects in this classification include virtual servers.
- Objects in this classification will be named using the following breakdown.
| Position | Description |
|---|---|
| 1-3 | Entity. For objects under control of the |
| 4-5 | Functions Code. The authorized options in this category are:AP - Application ServerAV - Anti-Virus ServerBE - Back End Mail ServerBG - Backup Gateway ServerBH - Bridgehead Mail ServerCA - Certificate Authority ServerDB - Database ServerDC - Domain ControllerDF - Distributed File System (DFS) ServerDH - Dynamic Host Configuration Protocol (DHCP)DN - Domain Name ServiceFE - Front End Mail ServerFS - File ServerFX - Fax ServerGA - Gateway / Bridge ServerGC - Global Catalog ServerLS - List ServerMD - Mobile DeviceML - Mail ServerMQ - Message Queue ServeGC - Global Catalog ServerML - Mail ServerMS - Media ServerNM - Network Management ServerPS - Print ServerPX - Proxy ServerRA - Remote Access ServerSM - System Management ServerSE - Security ServerWS - Web ServerVM - Voice MessagingVP - Voice Processor |
| 6-7 | Department – The 3 digit code that identifies the activity or agency assigned the device for usage. If the device is a shared device, then the primary agency responsible for its proper usage will be identified. |
| 8-10 | Site Code. The 3 digit code identifies the city. Here is a good reference for CA city name codes: http://www.dot.ca.gov/hq/structur/strmaint/brlog/table_c.htm This site has some cities with 4 character abbreviations, but in order to maintain the overall consistency with other areas of this document, use only 3 characters. |
| 11-15 | Virtual Machine Session ID: This number begins with VM and contains 3 additional digits to represent the unique identification for the virtual machines session at that location (e.g. VM021). |
Example Virtual Server Name
Naming Standards for Network Infrastructure:¶
- Objects in this classification include switches, firewalls and routers.
- Objects in this classification will be named using the following breakdown.
| Position | Description |
|---|---|
| 1-3 | Entity. For objects under control of the |
| 4-5 | Functions Code. The authorized options in this category are:FW - FirewallGW - VoIP Gateway RouterRT - RouterSW - Switch |
| 6-7 | Department – The 3 digit code that identifies the activity or agency assigned the device for usage. If the device is a shared device, then the primary agency responsible for its proper usage will be identified. |
| 8-10 | Site Code. The 3 digit code identifies the city. Here is a good reference for CA city name codes: http://www.dot.ca.gov/hq/structur/strmaint/brlog/table_c.htm This site has some cities with 4 character abbreviations, but in order to maintain the overall consistency with other areas of this document, use only 3 characters. |
| 11-15 | Asset Tag. The 5 digit code that reflects the official |
Example Network Infrastructure Name
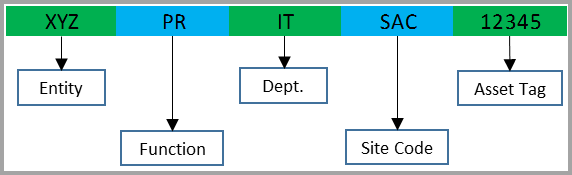
Naming Standards for Network Peripherals:¶
- Objects in this classification include network devices, such as printers.
- Objects in this classification will be named using the following breakdown.
| Position | Description |
|---|---|
| 1-3 | Entity. For objects under control of the |
| 4-5 | Functions Code. The authorized options in this category are:DM - Monitoring Device for HVAC / Environmental statusDS - Stand Alone Digital SendersPL - PlotterPR - Printers or Multi-function Print Devices (MFP)SC - Security Device, such as door badge system |
| 6-7 | Department – The 3 digit code that identifies the activity or agency assigned the device for usage. If the device is a shared device, then the primary agency responsible for its proper usage will be identified. |
| 8-10 | Site Code. The 3 digit code identifies the city. Here is a good reference for CA city name codes: http://www.dot.ca.gov/hq/structur/strmaint/brlog/table_c.htm This site has some cities with 4 character abbreviations, but in order to maintain the overall consistency with other areas of this document, use only 3 characters. |
| 11-15 | Asset Tag. The 5 digit code that reflects the official |
Example Network Peripherals Name
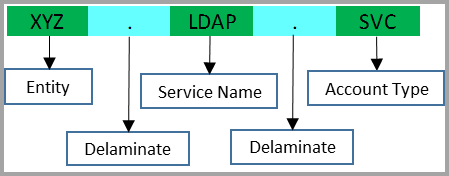
Naming Standards for Service Accounts:¶
- Objects in this classification include any accounts that are used to run services or processes on server systems. The overall length of service accounts should be no longer than 15 characters to comply with the NetBIOS limitation.
- Objects in this classification will be named using the following breakdown.
| Position | Description |
|---|---|
| 1-3 | Entity Code. For objects under control of the |
| 4 | This position will use a "." to delimit the different positions. |
| 5-11 | Service Name. This will generally be a friendly name to identify what the service account is used for. |
| 12 | This position will use a "." to delimit the different positions. |
| 13-15 | Account Type. The 3 digit code will identify the Active Directory accounts use. The authorized options in this category are:SVC - Service AccountTSK - Scheduled Task |
Example Service Account Name
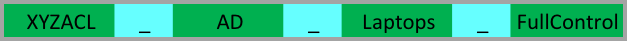
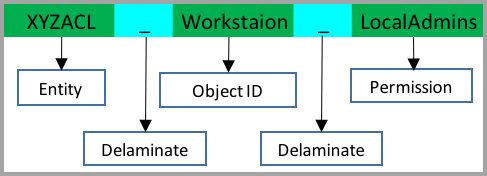
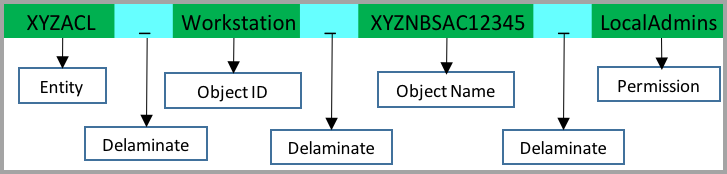
Naming Standards for Security Groups used as Access Control Lists (ACL):¶
- Objects in this classification include any Security Groups that are applied directly to an object, or used by any device referencing an LDAP group for permissions. These should always be Domain Local Groups.
- Objects in this classification will be named using the following breakdown.
| Position | Description |
|---|---|
| 1-6 | Security Group Type. For objects under control of the < Entity Code Security Group Type >, the example code for this document is "XYZACL". |
| 7 | This position will use a "_" to delimit the different positions. |
| 8-X | Object Identifier. This will generally be a friendly name to identify what the object is used for. Try to make the Object Identifier as descriptive as possible and unique for each object you might apply permissions to.AD - Active Directory Delegation of OUGPO - Group Policy Object e.g. Security Filtering of GPOFile - Network File Server Shared FolderWorkstation - Local Groups of Workstation e.g. Built-in Administrators Group (Workstation or Laptop)Network - Network device access. e.g. router and switchServer - Local Groups of Server e.g. Built-in Administrators GroupSPSite - Sharepoint SiteSPList - Sharepoint ListSPLibrary - Sharepoint Document RepositoryVMWare - VMWare permission delegation |
| X-X | This position will use a "_" to delimit the different positions |
| X-X | Object Name. This will be the friendly name of the object. e.g. OU Name, GPO Name, Folder Name. This field is not required if the object is being applied to all objects (for example: XYZACL_Workstation_LocalAdmins ). Additionally, an Object Name would be necessary if the group is being applied to only one system, (for example: XYZACL_Workstation_XYZNBSAC12345_LocalAdmins ). |
| X-X | Permission. The permission will identify exact permission that the ACL is used (e.g. FullControl, Modify, LocalAdmins ). Try to make the permission as descriptive as possible. |
Example Security group that has delegated control of the Laptops OU
Example Security group that is added to the built-in Administrators Group of all client systems.
Example Security group that is added to the built-in Administrators Group of one client system.
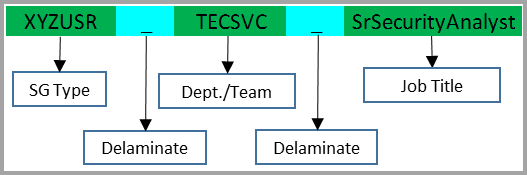
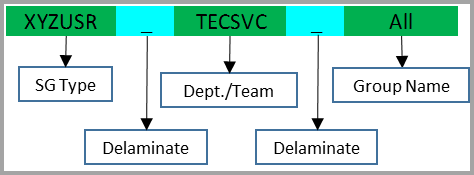
Naming Standards for Security Groups that contain users:¶
- Objects in this classification include any Security Groups that are applied directly to an object, or used by any device referencing an LDAP group for permissions. These should always be Domain Local Groups.
- Objects in this classification will be named using the following breakdown.
| Position | Description |
|---|---|
| 1-6 | Security Group Type. For objects under control of the < Entity > domain. The example code for this document is "XYZUSR". |
| 7 | This position will use a "_" to delimit the different positions. |
| 8-13 | Department/Team. This is the six digit code for the department and team. There is no set standard, each Entity will have to derive their own set of abbreviations. The first three digits should indicate the Department and the last three digits would be the sub team with-in the department, if it exists. Below are some examples.TECSVC - Technical ServicesHRSBEN - Human Resources Benefits SectionEXECUT - Executive Suite. E.g. CEO, CIOBRDDIR - Board of Directors |
| 14 | This position will use a "_" to delimit the different positions. |
| 15-X | Job Title. This will be the friendly job title of the employee. It should be based off the Human Resources position title document. |
Example of Security group User Job Title
Example of Security Group User for department "all" groups. In order to facilitate combining all the users in one department there should be a group that all the job title groups can be combined into.
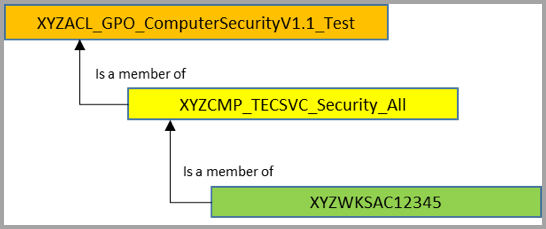
Naming Standards for Security Groups that contain computers:¶
- Objects in this classification include any Security Groups that are applied directly to an object, or used by any device referencing an LDAP group for permissions. These should always be Domain Local Groups.
- Objects in this classification will be named using the following breakdown.
| Position | Description |
|---|---|
| 1-6 | Security Group Type. For objects under control of the < Entity > domain. The example code for this document is "XYZCMP". |
| 7 | This position will use a "_" to delimit the different positions. |
| 8-13 | Department/Team. This is the six digit code for the department and team. There is no set standard, each Entity will have to derive their own set of abbreviations. The first three digits should indicate the Department and the last three digits would be the sub team with-in the department, if it exists. Below are some examples.TECSVC - Technical ServicesHUMRES - Human ResourcesEXECUT - Executive Suite. e.g. CEO, CIOBRDDIR - Board of Directors |
| 14 | This position will use a "_" to delimit the different positions. |
| 15-X | Group Designation. This will be the friendly group name. e.g. "All" or "Test". |
Example of Security Group Computers

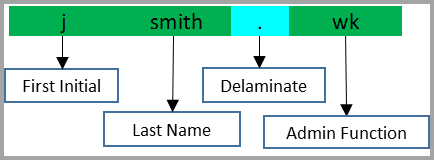
Administrator account naming convention:¶
- Objects in this classification include any domain accounts that are used in an administrative capacity.
- Objects in this classification will be named using the following breakdown.
| Position | Description |
|---|---|
| 1 | First Initial. This position should be the first name initial. |
| 2-X | Last Name. These positions should be the last name. |
| X | This position will use a "." to delimit the different positions |
| X-X | Admin Function. These last two characters indicate what administrative function the account is used for.wk - Workstation Administratorsv - Server Administratordc - Domain Administratornd - Network Administrator e.g. router/switch accountadmin - Security appliance Administrator |
Example Client Administrator account name
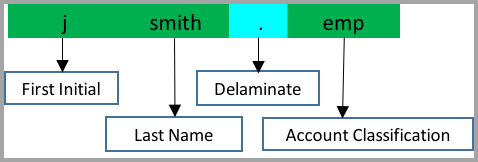
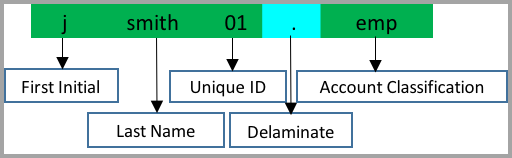
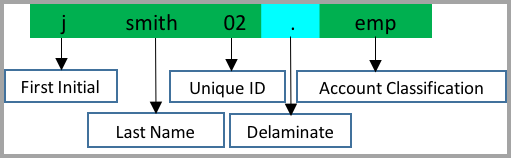
User account naming convention:¶
- Objects in this classification include any standard user accounts.
- Objects in this classification will be named using the following breakdown.
| Position | Description |
|---|---|
| 1 | First Initial. This position should be the first name initial. |
| 2-X | Last Name. These positions should be the last name. |
| X | This position will use a "." To delimit the different positions. |
| X-X | Account Classification. These three characters will be used to indicate the user type for purposes of any special restrictions that might need to be applied.emp - Employeectr - Contractorven - Vendorvol - Volunteerint - Intern |
| X-X | Unique Identifier. This is an optional field and is only used if two or more people have the same first initial and last name.01-99 - Second and subsequent accounts |
Examples of standard employee user account
Examples of second standard employee user account for users with the same name
Examples of third standard employee user account for users with the same name
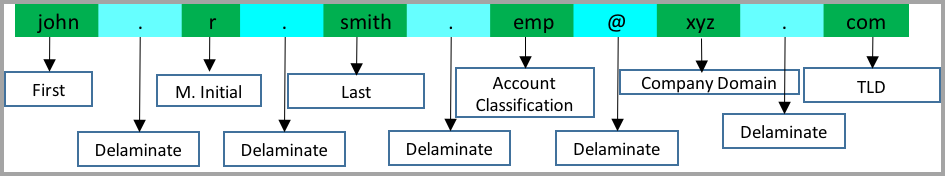
User account email address naming convention:¶
- Objects in this classification include any standard user email accounts.
- Objects in this classification will be named using the following breakdown.
| Position | Description |
|---|---|
| 1-X | First Name. This position should be the first name. |
| X | This position will use a "." to delimit the different positions. |
| X | Middle Initial. This positions should be the middle initial. (If no middle initial just place a single "." Between first and last |
| X | This position will use a "." to delimit the different positions. |
| X-X | Last Name. This position should be the last name. |
| X | This position will use a "." to delimit the different positions. |
| X-X | Account Classification. These three characters will be used to indicate the user type for purposes of any special restrictions that might need to be applied.emp - Employeectr - Contractorven - Vendorvol - Volunteerint - Intern |
| X | This position will use a "@" to delimit the start of the email domain. |
| X-X | Company Domain Name. For the purposes of this document "XYZ" will be used. |
| X | This position will use a "." to delimit the different positions. |
| X-X | TLD. This position is the top level domain name of "com" |
Example of standard user email account naming breakdown
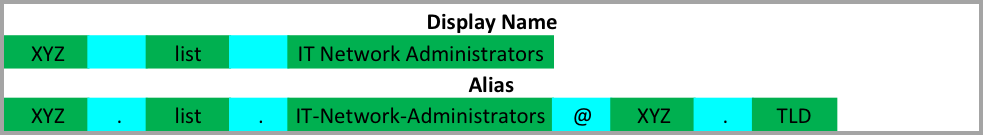
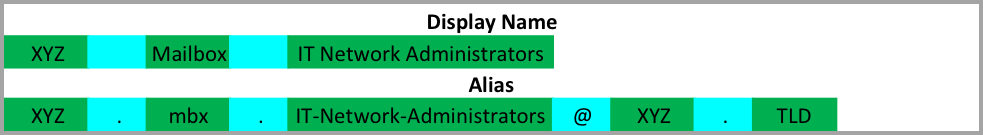
Distribution List and Organizational Mailbox naming convention:¶
- Objects in this classification include any distribution lists and Organizational Mailboxes.
- Objects in this classification will be named using the following breakdown.
| Position | Description |
|---|---|
| 1-3 | Agency Code. For the purposes of this document "XYZ" will be used. |
| 4 | In the Display name field this position will use a " " to delimit the different positions. In the Alias name field this position will use a "." to delimit the different positions. |
| 5-X | Object Type. These positions will indicate whether the object is a Distribution List or Organizational Mailbox.Distribution List. This position will use "list" to indicate the object is a distribution list.Organizational Mailbox. In the Display name field this position will use "Mailbox" and "mbx" in the alias field. |
| X | In the Display name field this position will use a " " to delimit the different positions.In the Alias name field this position will use a "." to delimit the different positions. |
| X-X | Object Name. This position should be the department name, abbreviation or friendly name of the distribution list. e.g. "IT Network Admins", "IT" "ISO", "IT HelpDesk", "IT System Admins". Each Object name should begin with the Department abbreviation when applicable. e.g "IT", "HR", "FIN" or contain a friendly generic name, such as:In the Display name field a " " will be used between words.In the Alias name field a "-" will be used between words. |
| X | This position will use a "@" to delimit the start of the email domain. |
| X-X | Company Domain Name. For the purposes of this document "XYZ" will be used. |
| X | This position will use a "." to delimit the different positions. |
| X-X | TLD. This position is the top level domain name of "com" |
Example of Distribution List
Example of Organizational Mailbox
Active Directory Sites and Services names:¶
- Objects in this classification include any Active Directory Sites that are created.
- Objects in this classification will be named using the following breakdown.
| Position | Description |
|---|---|
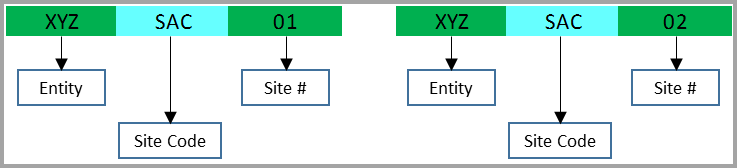
| 1-3 | Entity Code. For objects under control of the < Entity > domain. The example code for this document is "XYZ". |
| 4-6 | Site Code. The 3 digit code that identifies the city. Here is a good reference for CA city name codes: http://www.dot.ca.gov/hq/structur/strmaint/brlog/table_c.htm This site has some cities with 4 character abbreviations, but in order to maintain the overall consistency with other areas of this document, use only 3 characters. |
| 7-8 | Site Number. This will identify any cities that might have multiple sites.01 - First or only site in a city02-99 - Second and subsequent sites in a city |
Example of Active Directory Sites and Services naming breakdown for a city with only one site.
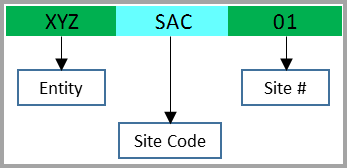
Example of Active Directory Sites and Services naming breakdown for a city with multiple sites.
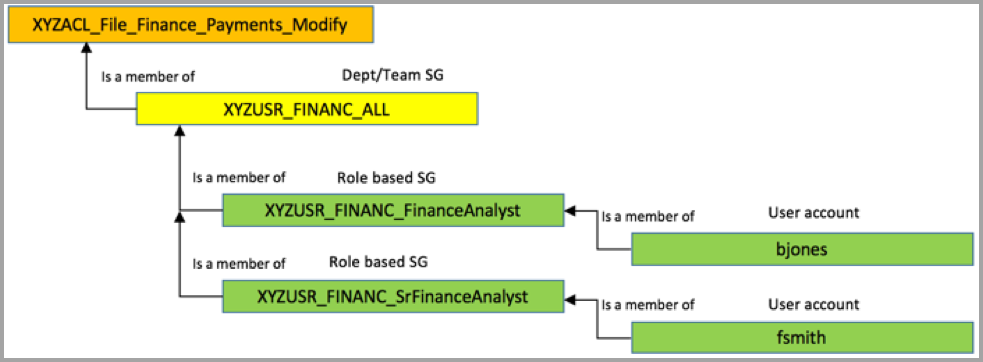
ACL, USR and CMP group examples of implementation:¶
This section is designed to provide an example for how to implement role based access. It can be used for both user and administrator delegation. Depending on the size of the organization, it could be very manpower intensive to implement, but provides a lot of value in the end. For the job title.
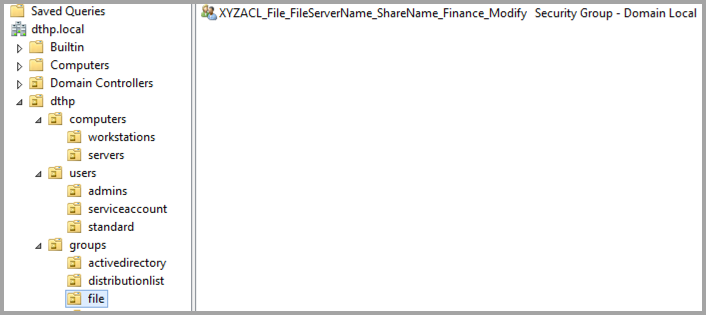
- File Share permissions – The XYZACL_ group is applied as NTFS permissions on a shared folder for a department, with the XYZUSR_ groups nested inside.
Example of Role Based security groups used on a file server
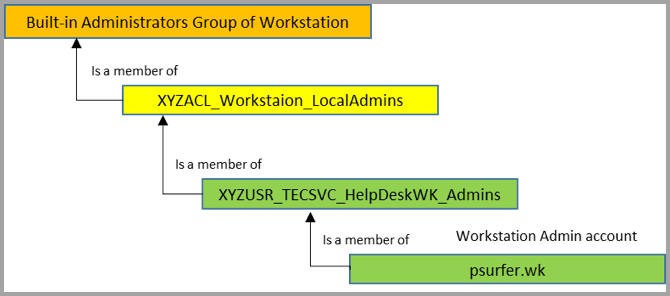
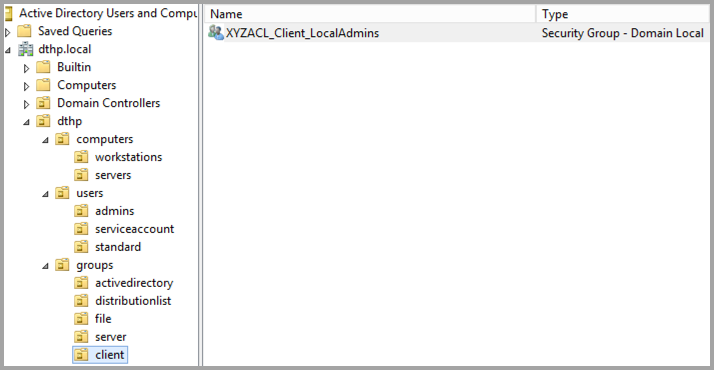
- Workstation Built-in Administrators group – The XYZACL_Workstation_LocalAdmins is added to the built-in Administrators group of every client using Group Policy Preferences (GPP), with the XYZUSR_ groupname, for the Help Desk Administrator accounts, nested inside.
Example of Role Based security group used for local administrative access of clients.
- Group Policy Permissions – This would allow the filtering of a GPO that is applied to only a specific group of computers. The same could be done for user accounts using USR groups.
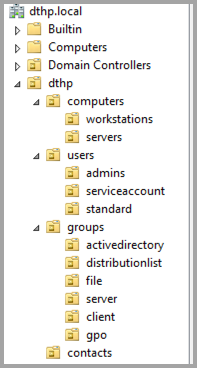
Active Directory OU Structure based on resources:¶
- This document is designed to give an example of an OU structure based on resources. Often times OU structure is designed by physical location but the objects are not treated any different from a security perspective. If the structure is designed using resources as a base, other sub OUs can created under each resource to further break down objects by physical location, department or function type if needed. This allows applying GPOs at the resource level so all objects have the base GPO, but still allows deviations by applying another GPO to the subordinate OU.
domain.com - orgname (I prefer to create a root level OU and create resource OUs under it. This makes for a cleaner interface. It is also usefull for a large enterprise that has multiple departments, each with their own IT department) - computers - clients - HR - IT - OPS - servers - Application - Database - Web - contacts - distributionlists - admin - organizational - securitygroups (Separating OUs by function allows easier delegation for different teams and also easier to find when manually searching) - activedirectory (These security groups should be used Active Directory delegations) - file (These security groups are used for NTFS permissions no network shares) - clients (These security groupts are used for local group access of client systems) - servers (These security groupts are used for local group access of server systems) - vmware (These security groups are used for vSphere/VMware delegation/access) - network (These security groups are used for access to network devices, i.e. in conjuction with Radius, TACACS and LDAP) - firewall (These security groups are used for access to firewall devices, i.e. in conjuction with Radius, TACACS and LDAP) - users - standard - admin - serviceaccount
Example OU structure
Example OU with security group for file share
Example OU with security group for client local administrator group
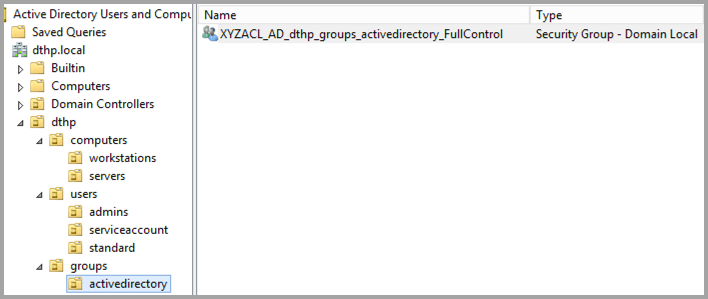
Example OU with security group for Active Directory delegation